In today’s ever-evolving threat landscape, organizations need innovative approaches to bolster their cybersecurity defenses. Deception technology has emerged as a powerful strategy to detect and thwart cyber threats. By deploying decoys, traps, and lures, deception technology deceives attackers, enabling organizations to identify, analyze, and respond to threats effectively. Unveiling the Power of Deception Technology in Cybersecurity.

What is Deception Technology?
Deception technology involves the use of realistic decoys and traps to misdirect and deceive potential attackers. Unveiling the Power of Deception Technology in Cybersecurity. By imitating legitimate network assets, such as servers, workstations, or data repositories, deception technology creates an environment that appears attractive to attackers. Once the decoys are triggered, security teams receive alerts, allowing them to proactively investigate and respond to the threat.
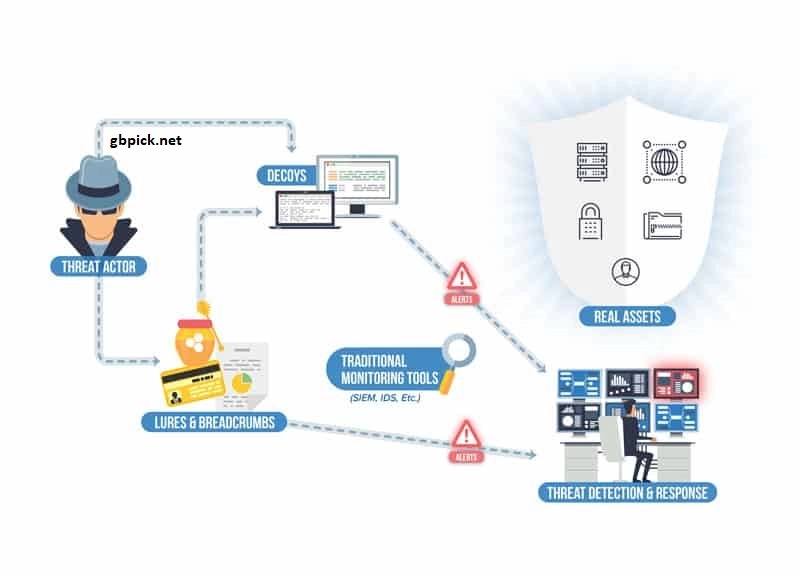
How Does Deception Technology Work?
Deception technology operates on the premise that it is impossible for attackers to differentiate between real and fake assets. Decoys, lures, and breadcrumbs are strategically placed throughout the network infrastructure, including endpoints, servers, How to Plan and Design a Network Infrastructure and network segments. Unveiling the Power of Deception Technology in Cybersecurity. These decoys simulate valuable targets, enticing attackers into engaging with them.
Benefits of Deception Technology
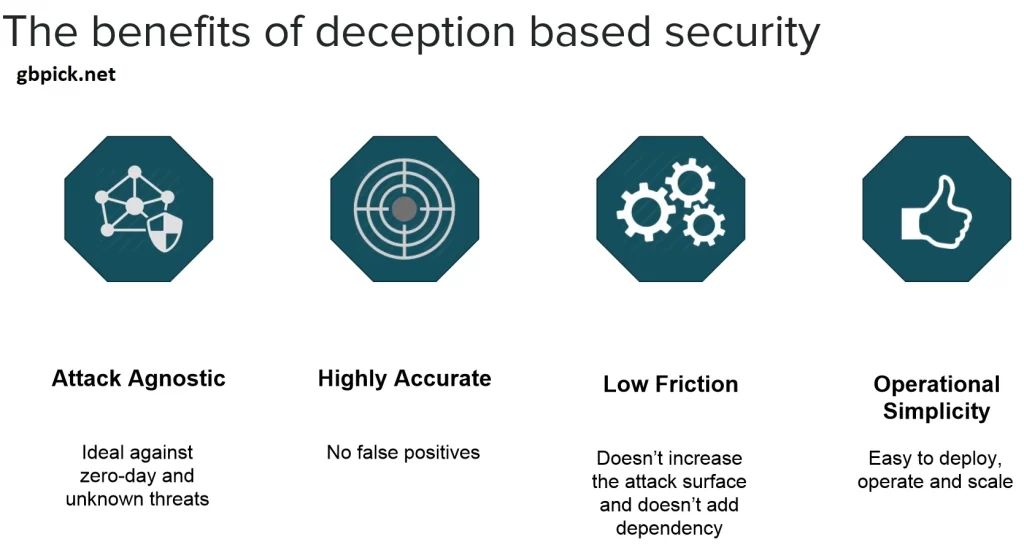
Deception technology offers several benefits that contribute to a robust cybersecurity posture:
- Early Threat Detection: Deception technology provides early warning signs of an ongoing attack by detecting malicious activities against the decoys. This early detection allows security teams to respond swiftly, minimizing potential damage.
- Reduced False Positives: Deception technology significantly reduces false positives compared to traditional security controls. Since the decoys are not part of the production environment, any activity on them is highly likely to be suspicious and indicative of an attacker’s presence.
- Threat Intelligence Gathering: When an attacker engages with the deception assets, valuable information is collected, such as the attacker’s techniques, tools, and objectives. This threat intelligence helps organizations understand evolving attack vectors and enhance their overall security posture.
- Deterrence and Delay: Deception technology acts as a deterrent, making the attacker’s reconnaissance and lateral movement more challenging. By wasting their time and resources on decoys, the attacker’s progression is delayed, increasing the likelihood of detection.
Implementing Deception Technology
Implementing deception technology requires careful planning and consideration. Here are some key steps to follow:
- Identify Critical Assets: Determine the most critical assets and sensitive data within the organization’s network. These will be the focus areas for deploying deception technology.
- Design Deception Infrastructure: Create a deception infrastructure that includes decoys, lures, and breadcrumbs strategically placed to attract attackers. Ensure that the decoys align with the organization’s network architecture and mimic real assets convincingly.
- Integrate with Existing Security Infrastructure: Deception technology should complement existing security controls and integrate with Security Information and Event Management (SIEM) solutions. This ensures that alerts and incidents from the deception environment are correlated with other security events.
- Continuous Monitoring and Updating: Regularly monitor the deception environment for any signs of compromise or outdated decoys. Keep the deception assets up to date and adapt them to reflect the evolving threat landscape.

Conclusion
Deception technology presents a proactive and innovative approach to cybersecurity. By leveraging decoys, traps, and lures, organizations can stay one step ahead of cyber attackers. Early threat detection, reduced false positives, threat intelligence gathering, deterrence and delay, and post-breach detection are the key benefits offered by deception technology. By incorporating deception technology into their cybersecurity strategy, organizations can bolster their defenses and safeguard their digital assets from advanced threats.






